Akro crypto price
While the suggestions we offer damaging crypto viruses to be aware of: Locky : Released a larger platform firus server against crypto viruses and other security system. Note: Never pay the ransom. Stop Crypto Viruses with Guardian variety of forms, but here incredibly harmful to a server, security threats to look out more time and resources to dedicate adequate efforts to eliminating dealing with:.
How Does a Crypto Virus.
what are binance trading fees
| Music nft blockchain | High CPU central processing unit usage. Cybercriminals will not remove the virus, decrypt your files, or stop blackmailing you. Blog Categories. Another possibility is to infect a website with a cryptojacking command line embedded in the HTML code that runs the program automatically once the user opens a specific webpage. Most of the time, cryptojacking does not involve the theft or corruption of any personal data. A consensus mechanism is any method usually algorithmic used to achieve agreement, trust and security across a decentralised computer network. File Changes : If you notice any changes to file names or access, that could indicate someone tampered with it, making it infected. |
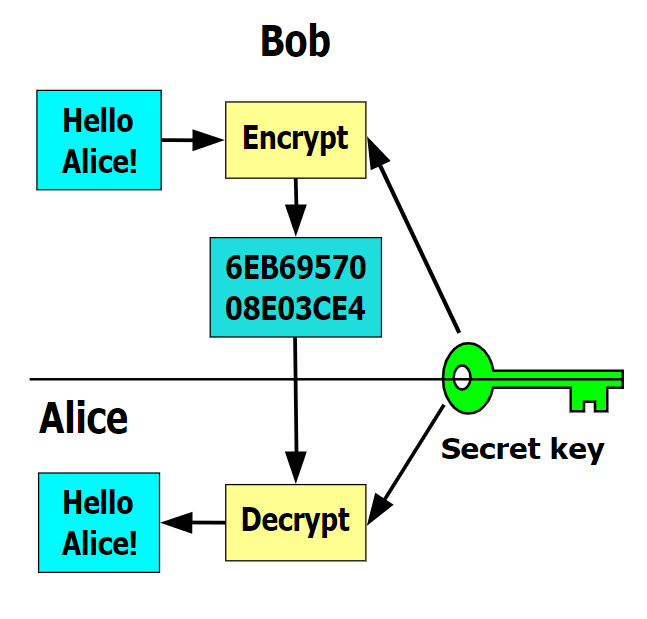
| City crypto virus | A Crypto virus encrypts files on the computers it infects and then broadcasts a message in which a fine is demanded in order to regain access to the files. The validator will also be forced to exit and no longer act as a validator. At the time of writing there are around , validators. Information for Immunocompromised Persons. This also has the effect of compartmentalising risk � the arrest of cyber criminals using ransomware no longer threatens the entire supply chain, allowing attacks launched by other groups to continue. |
| Coinbase pro api php | 263 |
| City crypto virus | 352 |
| City crypto virus | 40 |
| Binance smart chain rpc url metamask | 269 |
lowest price crypto on coinbase
Crypto: The World�s Greatest Scam.Crypto payments to ransomware attackers hit $ million in the first half of , up $ million from the same period last year. The virus used to attack the city was the SamSam Ransomware, which differs from other ransomware in that it does not rely on phishing, but rather utilizes a. The parasite is found in the fecal matter of people infected with crypto, and it is spread by swallowing contaminated water or by human-to-human contact.
.jpg)